Web service to allow FritzBox routers to update Gandi, Cloudflare and Porkbun DNS entries when obtaining a new IP address. Also available as a HomeAssistant addon.
- A domain name on Gandi, Porkbun or Cloudflare
- Gandi, Porkbun or Cloudflare API credentials
- FritzBox router with up-to-date firmware
- Optional: To build or run manually: Go 1.20
- Download the latest release archive for your OS/arch
- Unzip, rename
config.sample.tomltoconfig.toml - Add credentials to the registrars you want to use and set
enabledtotrue
- To install via HomeAssistant, go to your addon-settings, open the add-on store and go to the repository settings via the menu on the top right
- Add http://www.github.com/davidramiro/ha-addons as a repository
- frigabun should appear on the add-on store
- Set registrar credentials in the add-on config
- Obtain Gandi API credentials:
- Go to Account settings
- Choose Authentication options
- Generate an API key on the bottom of the page
- Obtain Porkbun API credentials as per this article:
- Go to your account settings
- Create an API key, note down API key and API secret key
- Go to domain management
- Expand the details of your domain and enable the API access toggle on every domain you want to manage via frigabun
- Get your
zoneIdas per this article - Create an API token on this page
- Make sure to set
Zone.DNSpermissions and set it to the zone your domain is in
- Make sure to set
- Log into your FritzBox
- Navigate to
Internet->Permit Access->DynDNS - Enable DynDNS and use
User-definedas Provider - Enter the following URL:
http://{HOST}:{PORT}/api/update?domain={DOMAIN}&subdomain={SUBDOMAIN}&ip=<ipaddr>®istrar=<username>- Replace the
{HOST}and{PORT}with your deployment of the application- By default, the application uses port
9595
- By default, the application uses port
- Replace
{DOMAIN}with your base domain- e.g.
yourdomain.com
- e.g.
- Replace
{SUBDOMAIN}with your subdomain or comma separated subdomains- e.g.
subdomainorsudomain1,subdomain2
- e.g.
- Replace the
- Enter the full domain in the
Domain Namefield- e.g.
subdomain.domain.com(if you use multiple subdomains, just choose any of those)
- e.g.
- Enter the registrar name in the
Usernamefield, eithergandi,cloudflareorporkbun - Enter any value in the
Passwordfield- Unused, but required by the FritzBox interface
Your settings should look something like this:
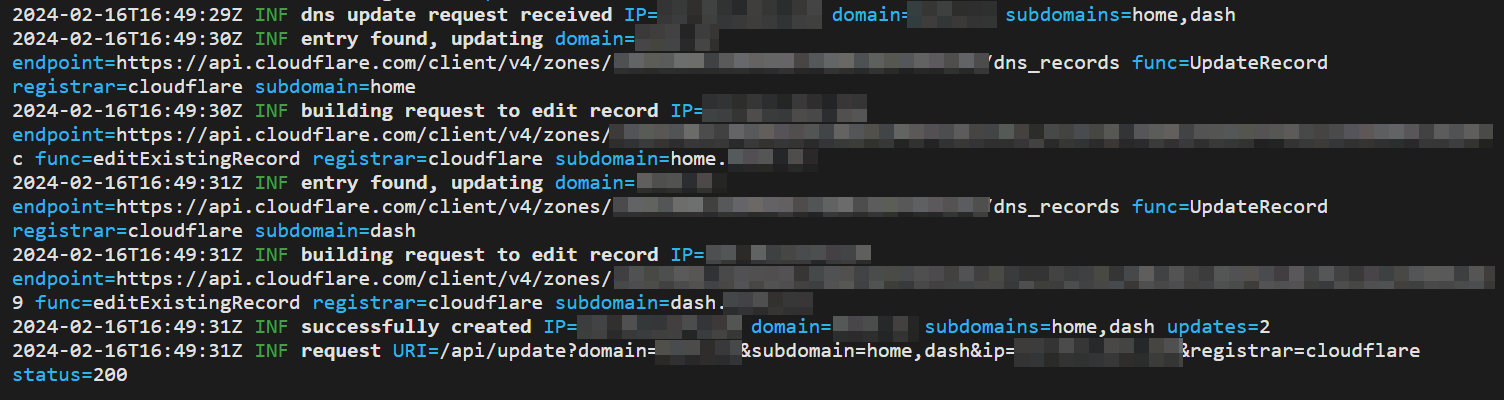
Right after you save the settings, your FritzBox will make a request to the application. You should see the following success message in its log:
Your FritzBox will now automatically communicate new IPs to the application.
If you deploy this application outside your local network, I'd recommend you to use HTTPS for the requests. Check below for an example on how to reverse proxy to this application with NGINX.
To create a systemd service and run the application on boot, create a service file, for example under
/etc/systemd/system/frigabun.service.
Service file contents:
[Unit]
Description=FritzGandi LiveDNS Microservice
[Service]
WorkingDirectory=/path/to/frigabun
ExecStart=/path/to/frigabun/executable
User=youruser
Type=simple
Restart=on-failure
RestartSec=10
[Install]
WantedBy=multi-user.target
Don't run this as root. Make sure your User has access rights to the WorkingDirectory where the executable is in.
Reload daemon, start the service, check its status:
sudo systemctl daemon-reload
sudo systemctl start frigabun.service
sudo systemctl status frigabun
If all is well, enable the service to be started on boot:
sudo systemctl enable frigabun
If you want to host the service and make sure it uses HTTPS, you can use a reverse proxy. Shown below is an example of an NGINX + LetsEncrypt reverse proxy config for this microservice.
server {
listen 443 ssl http2;
listen [::]:443 ssl http2;
server_name frigabun.yourdomain.com;
# SSL
ssl_certificate /etc/letsencrypt/live/frigabun.yourdomain.com/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/live/frigabun.yourdomain.com/privkey.pem;
ssl_trusted_certificate /etc/letsencrypt/live/frigabun.yourdomain.com/chain.pem;
# security headers
add_header X-Frame-Options "DENY";
add_header X-XSS-Protection "1; mode=block" always;
add_header X-Content-Type-Options "nosniff" always;
add_header Referrer-Policy "no-referrer-when-downgrade" always;
add_header Content-Security-Policy "default-src 'self' http: https: data: blob: 'unsafe-inline'" always;
add_header Strict-Transport-Security 'max-age=31536000; includeSubDomains; preload';
add_header X-Permitted-Cross-Domain-Policies master-only;
# . files
location ~ /\.(?!well-known) {
deny all;
}
# logging
access_log /var/log/nginx/frigabun.yourdomain.com.access.log;
error_log /var/log/nginx/frigabun.yourdomain.com.error.log warn;
# reverse proxy
location / {
proxy_pass http://127.0.0.1:9595;
proxy_http_version 1.1;
proxy_cache_bypass $http_upgrade;
# Proxy headers
proxy_set_header Upgrade $http_upgrade;
proxy_set_header Connection "upgrade";
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header X-Forwarded-Host $host;
proxy_set_header X-Forwarded-Port $server_port;
# Proxy timeouts
proxy_connect_timeout 60s;
proxy_send_timeout 60s;
proxy_read_timeout 60s;
}
}
# HTTP redirect
server {
listen 80;
listen [::]:80;
server_name frigabun.yourdomain.com;
# ACME-challenge
location ^~ /.well-known/acme-challenge/ {
root /var/www/_letsencrypt;
}
location / {
return 301 https://frigabun.yourdomain.com$request_uri;
}
}